Grayscale images of DoS (a), DDoS (b), PortScan (c), FTP-Patator (d),... | Download Scientific Diagram
Fast Port Scanner Download - Scans about 400 ports a second. It supports both the TCP/IP and UDP protocols. Select address range

Sac À Dos Scan Smart Demon Slayer Blade My Wife Zen Yi Ordinateur Portable Grande Capacité Résistant À l'eau D'ordinateur avec Port USB pour Hommes Et Femmes Loisirs : Amazon.fr: Informatique
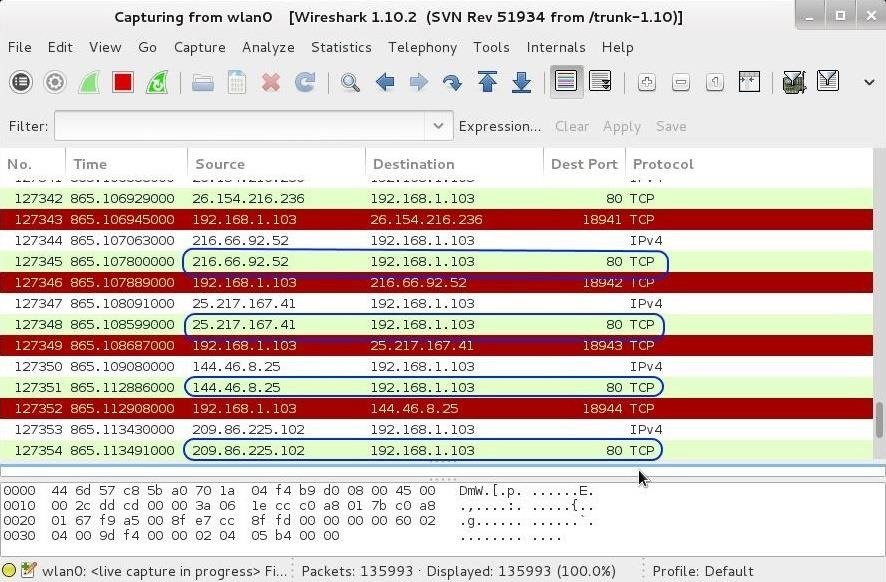
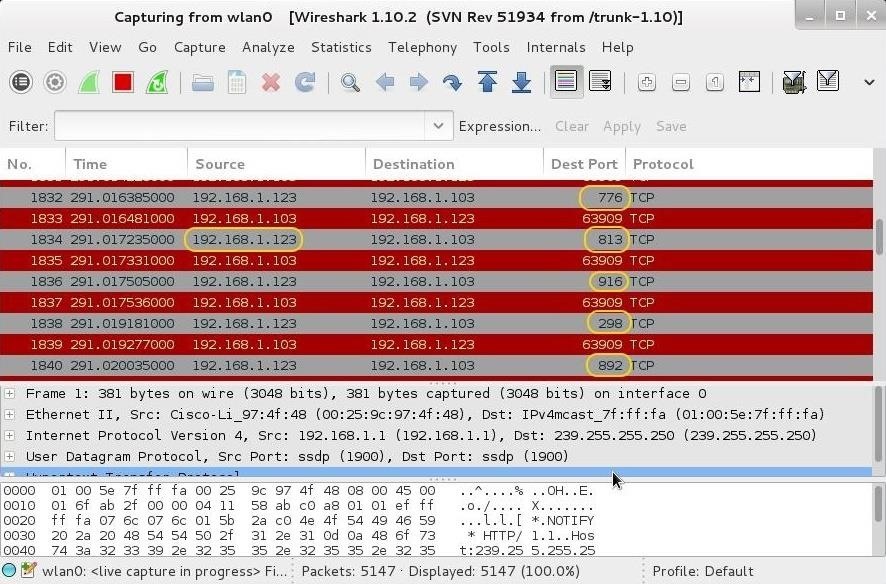
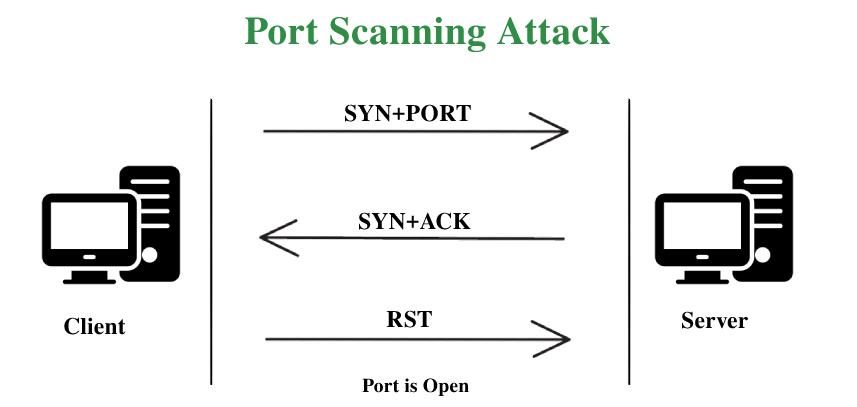
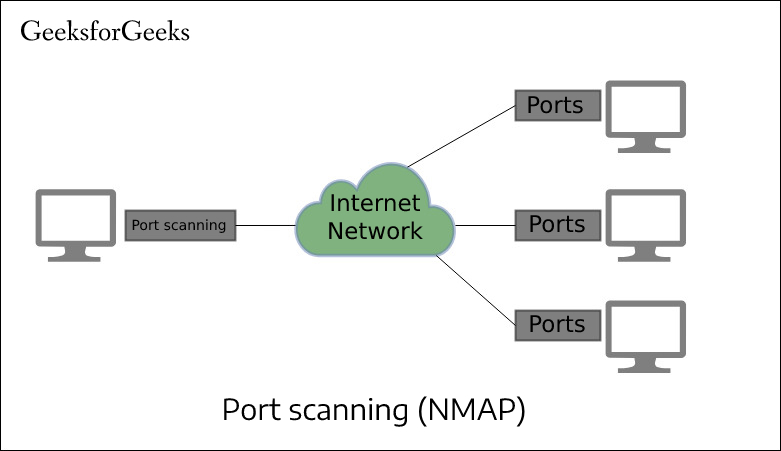
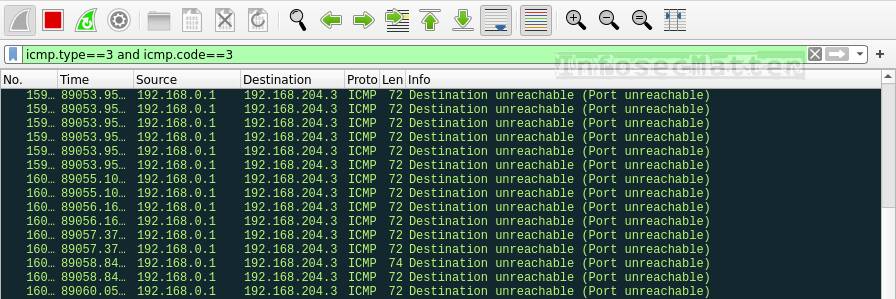
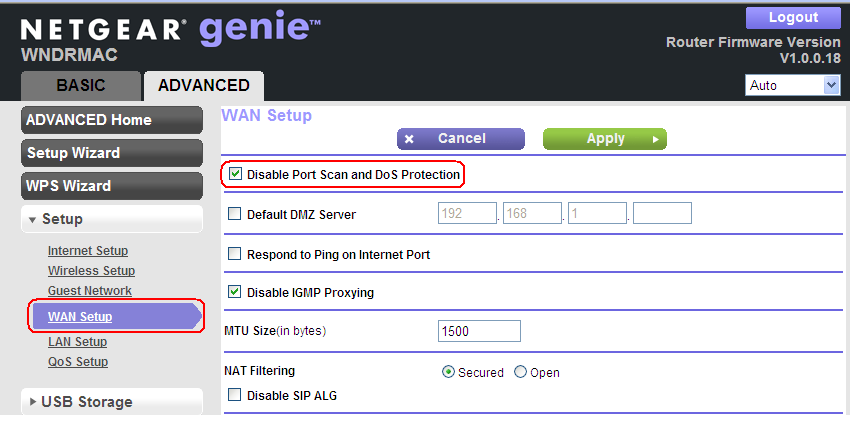
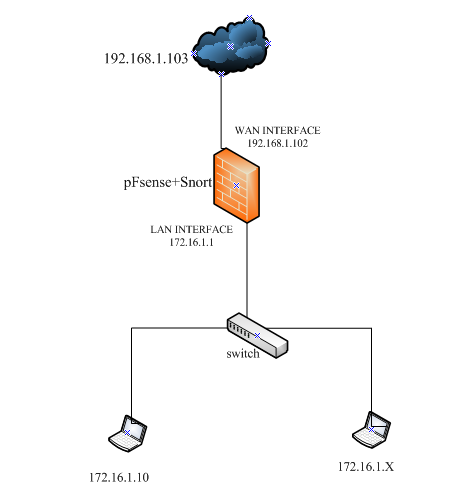
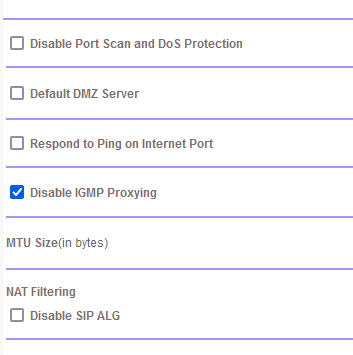
Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 10 (Identifying Signatures of a Port Scan & DoS Attack) « Null Byte :: WonderHowTo

Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 10 (Identifying Signatures of a Port Scan & DoS Attack) « Null Byte :: WonderHowTo